This article presents Data Governance from Closeloop's perspective, describing how governance is embedded into discovery, architecture, development, integrations, security, testing, deployment, reporting, AI readiness, and continuous improvement.
Executive Overview
In today's digital-first world, data is one of the most valuable assets an organization owns. Every customer interaction, business workflow, application, integration, and analytics system generates data that can influence decision-making, operational efficiency, customer experience, and long-term business growth.
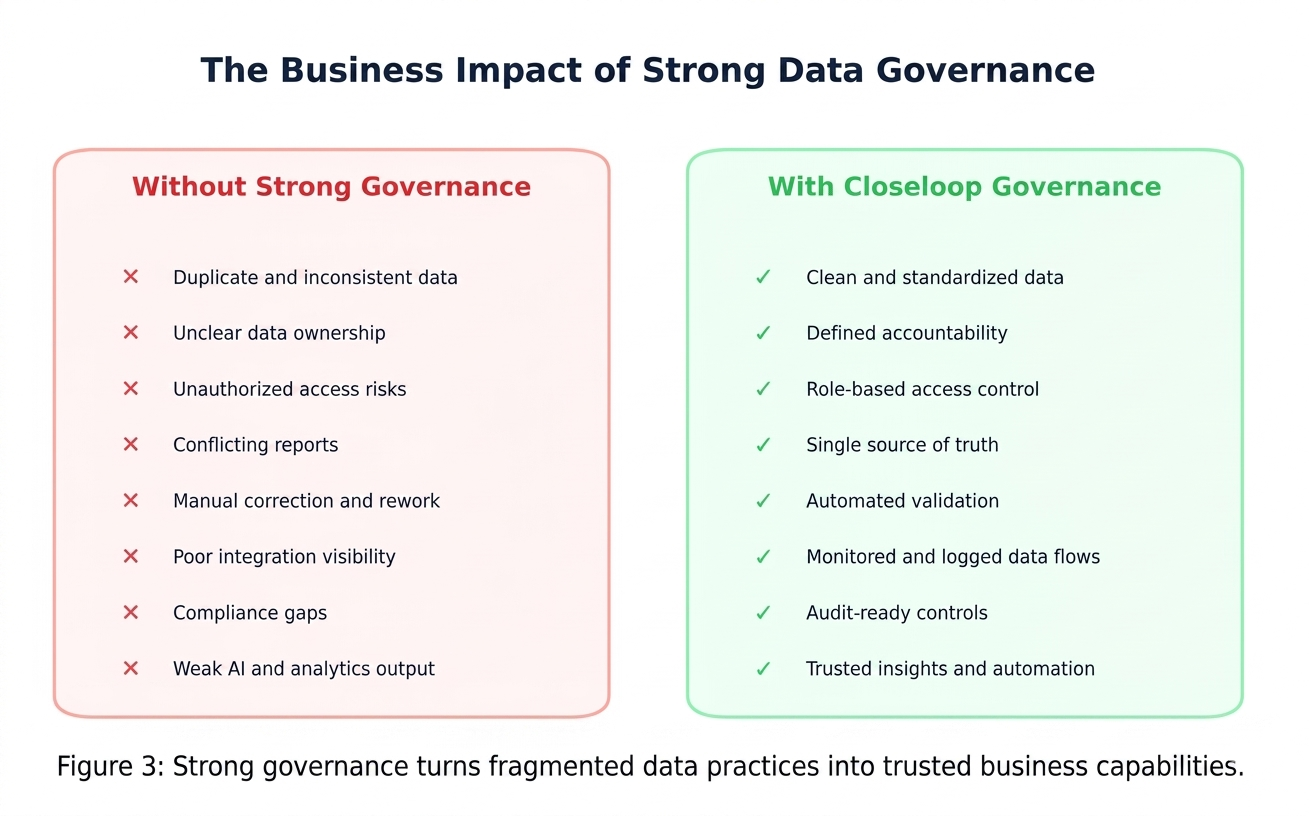
However, data only creates value when it is accurate, secure, accessible to the right people, protected from misuse, and governed through clear standards. Without strong data governance, organizations can face fragmented systems, inconsistent reporting, compliance risks, security vulnerabilities, and loss of stakeholder trust.
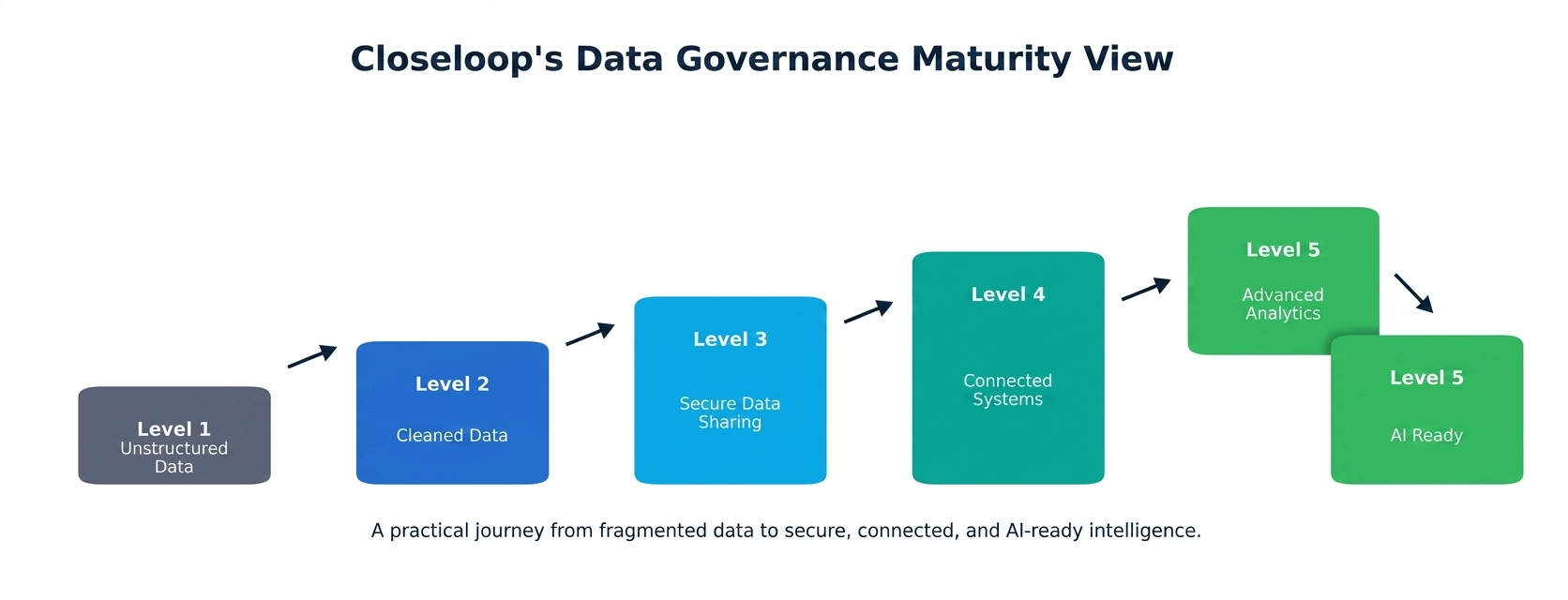
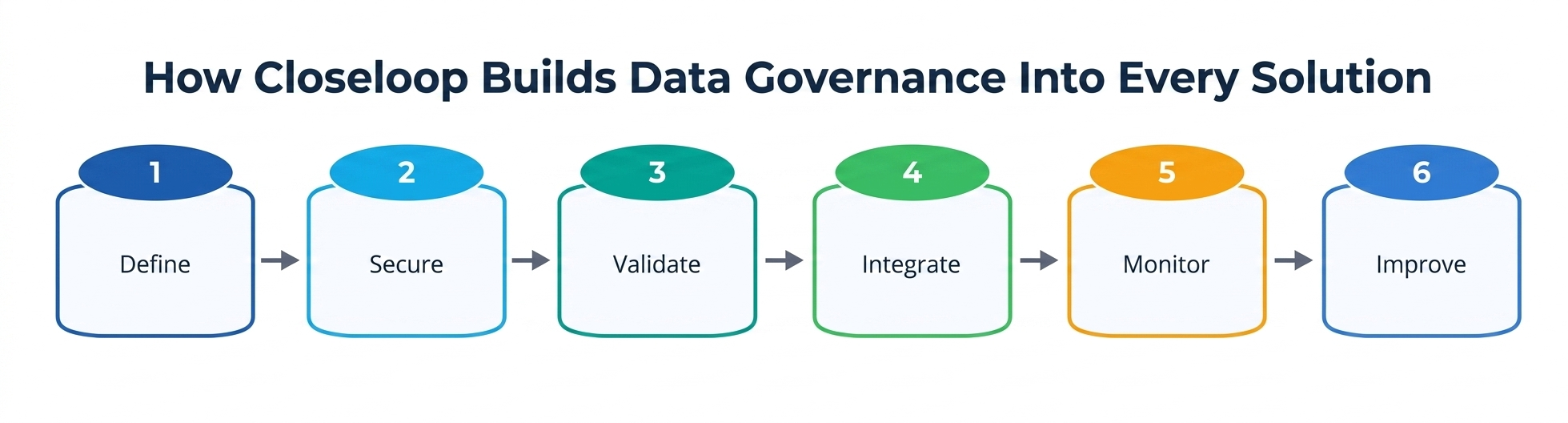
At Closeloop, data governance is not treated as a one-time policy or a back-office compliance activity. It is embedded into how we design, build, integrate, deploy, and maintain digital solutions for our clients. Whether we are developing custom software, modernizing enterprise platforms, integrating CRM and ERP systems, building analytics solutions, or enabling AI-driven workflows, we ensure that data is handled responsibly across its full lifecycle.
For us, data governance means creating a structured, secure, and accountable approach to managing data so that it remains trustworthy, compliant, and business-ready.
What Data Governance Means at Closeloop
At Closeloop, data governance is the framework of principles, processes, roles, controls, and technologies that guide how data is collected, stored, accessed, processed, shared, retained, and protected. Under our governance model, data is:
- Accurate and consistent across systems
- Secure from unauthorized access or misuse
- Available to the right users at the right time
- Compliant with applicable regulations and business requirements
- Traceable across applications, workflows, and integrations
- Managed with clear ownership and accountability
- Used ethically and responsibly
Our approach goes beyond technical data management. We view data governance as a shared responsibility between business, technology, security, compliance, and delivery teams. This helps ensure that every solution we deliver is not only functional, but also reliable, scalable, secure, and ready for future growth.
Why Data Governance Matters
Businesses today operate in a complex data environment. Customer data may flow through websites, mobile apps, CRMs, ERPs, payment gateways, analytics platforms, marketing automation tools, support systems, and cloud infrastructure. If governance is weak, even a technically strong system can create operational and compliance challenges.
Strong data governance helps organizations:
- Improve decision-making with reliable and consistent data
- Reduce risks related to privacy, compliance, and security
- Maintain customer trust by protecting sensitive information
- Improve integration quality across multiple business systems
- Enable better reporting, analytics, and forecasting
- Support AI and automation with clean, well-structured data
- Reduce duplication, errors, and manual rework
- Create accountability for how data is handled
Core Principles of Data Governance at Closeloop
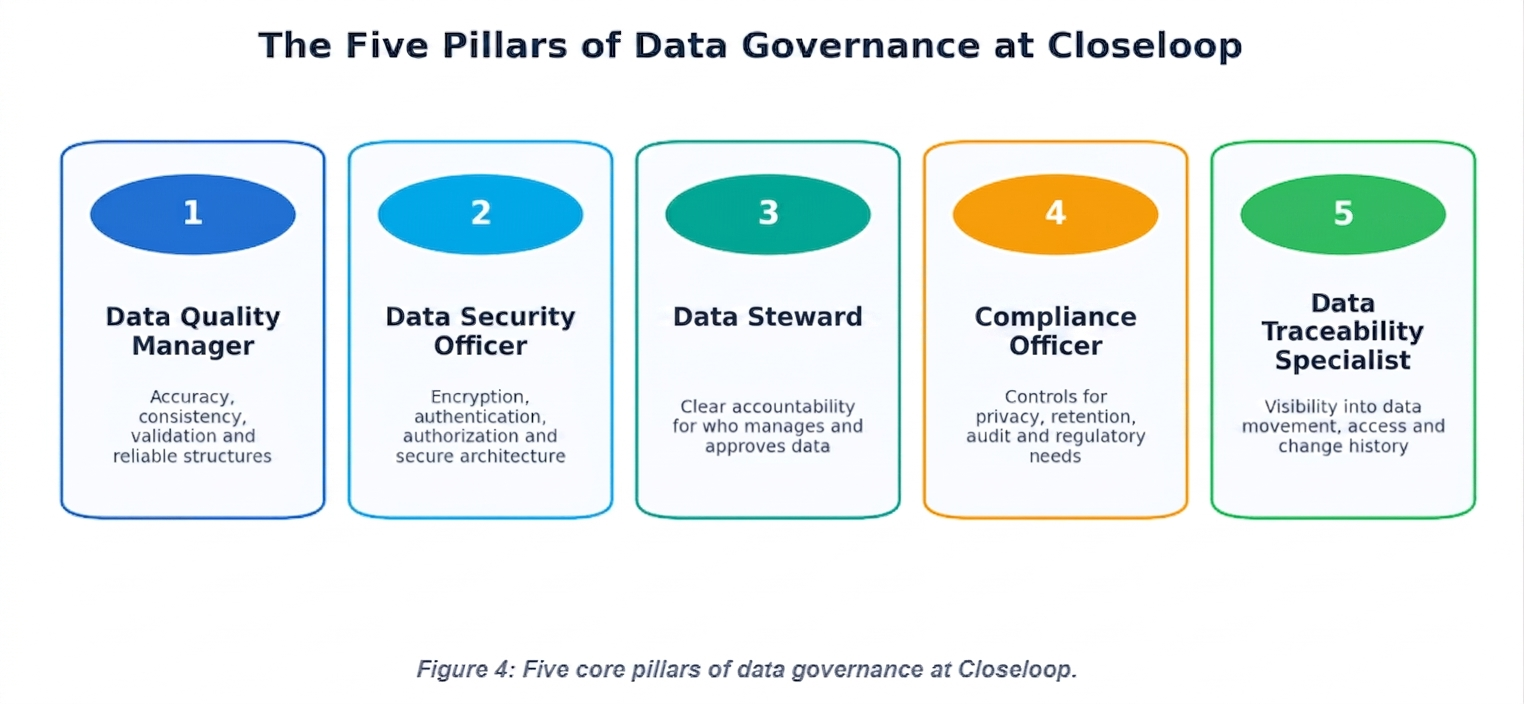
Data Ownership and Accountability
Every successful data governance model begins with ownership. At Closeloop, we define clear responsibility for data across systems, modules, workflows, and integrations. This includes identifying who owns the data, who can access it, who can modify it, who is responsible for validating it, and who approves its movement between systems. Clear ownership helps prevent confusion, improves decision-making, and ensures that data-related changes are reviewed by the right people.
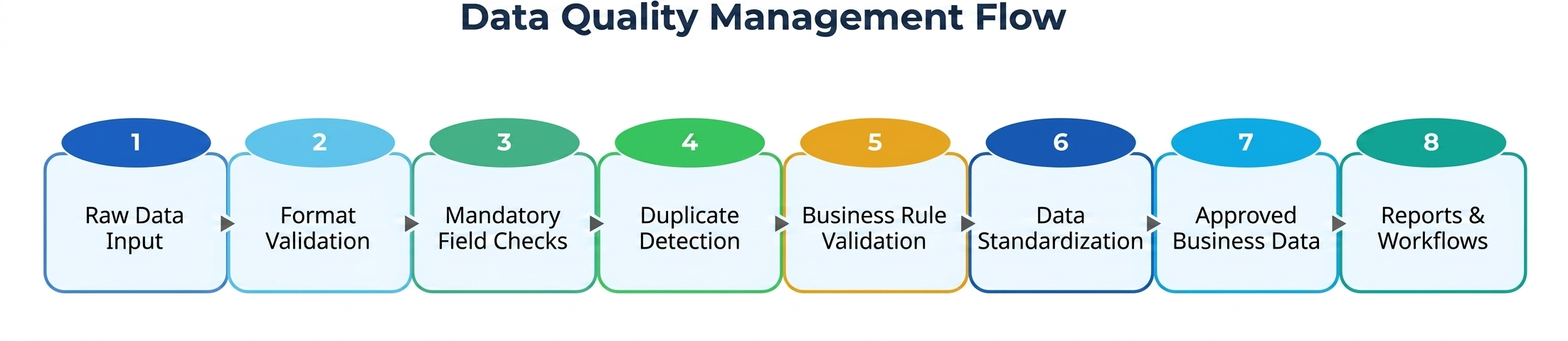
Data Quality and Accuracy
Poor-quality data can lead to poor business decisions. That is why Closeloop focuses on data quality from the earliest stages of solution design. We apply validation rules, mandatory field checks, formatting standards, deduplication logic, business rule enforcement, and structured data models to improve accuracy and consistency.
Security by Design
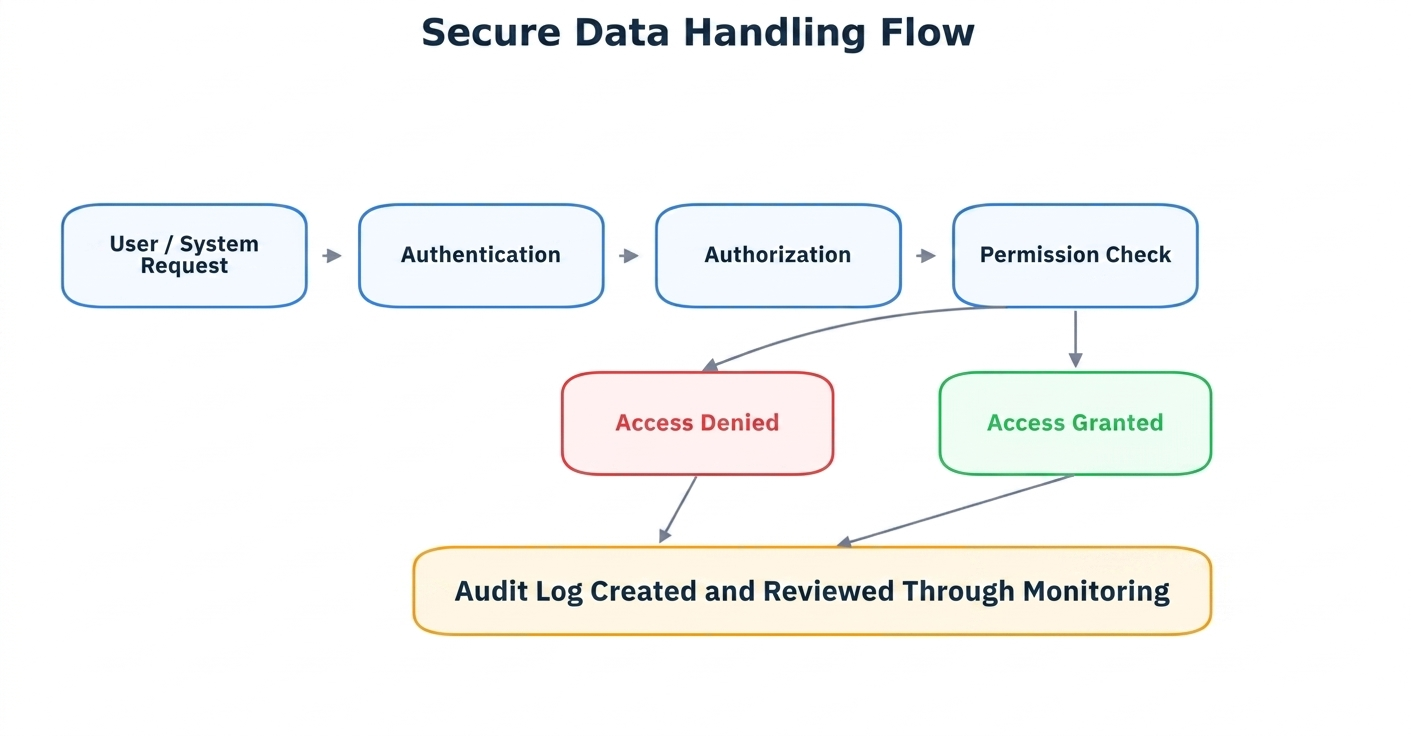
Data governance cannot exist without strong security. At Closeloop, security is built into the solution architecture rather than added at the end of the development cycle. We follow security-by-design practices that include role-based access control, authentication, authorization, encryption, secure APIs, audit trails, secure coding standards, and environment-specific access restrictions.
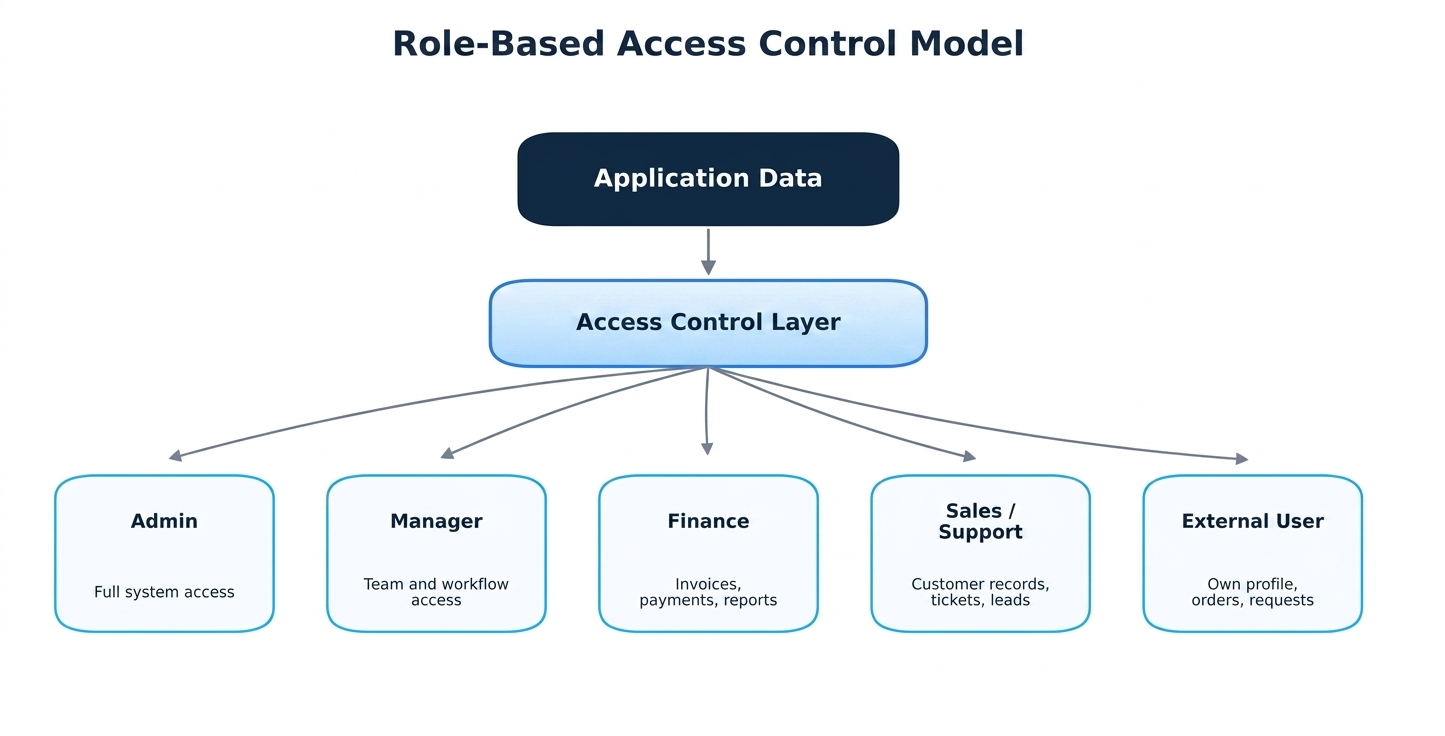
Role-Based Access and Permission Management
Access control is one of the most important parts of data governance. At Closeloop, we design systems with well-defined roles and permissions so that data access is controlled, transparent, and manageable. Each role is mapped to permissions such as view, create, edit, approve, export, delete, upload, download, or manage records.
Compliance and Regulatory Readiness
Data governance must align with applicable regulatory and industry requirements. At Closeloop, we design and deliver solutions with compliance awareness from the beginning. Our governance approach supports consent management, data minimization, access logs, auditability, secure data retention, deletion workflows, and controlled sharing of sensitive information.
Data Lifecycle Management
Data has a lifecycle — it is created, used, updated, shared, archived, and eventually deleted or retained based on business and legal requirements. Closeloop helps define how data is captured, stored, accessed, retained, archived, backed up, restored, and deleted across its complete journey.
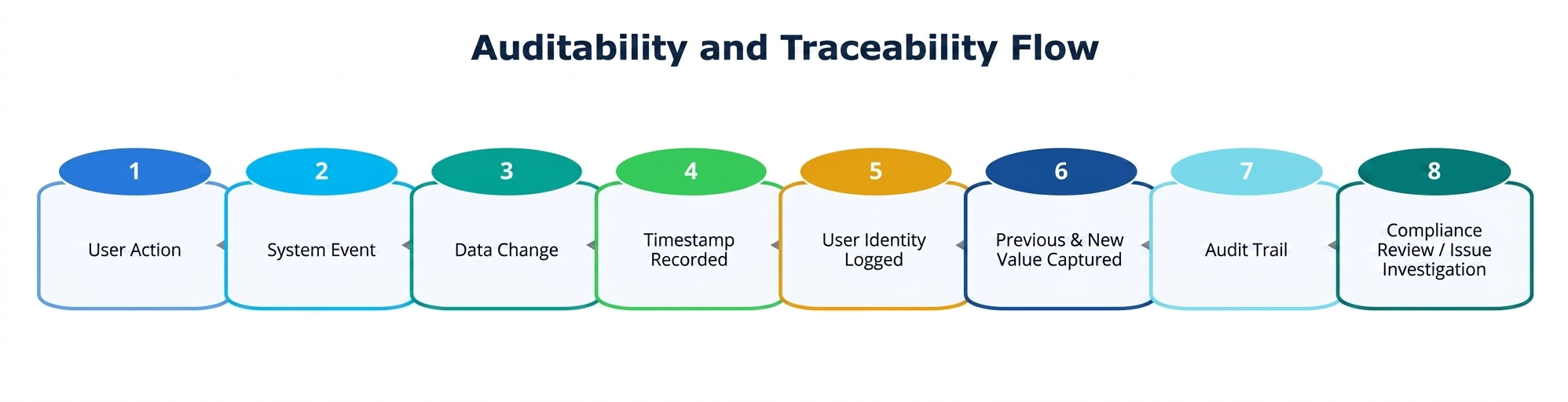
Auditability and Traceability
For enterprise-grade systems, organizations must know how data changed, who changed it, when it changed, and why it changed. Closeloop enables auditability through logs, activity tracking, change history, approval workflows, and system monitoring.
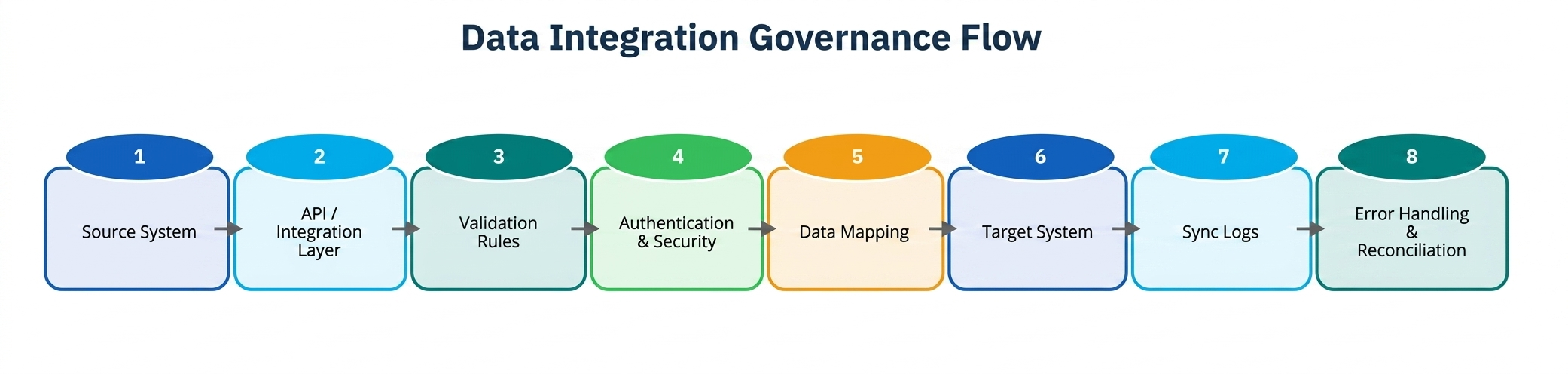
Data Integration Governance
Modern organizations rarely operate on a single platform. At Closeloop, we define the source of truth, data mapping rules, synchronization frequency, error handling, API security, retry logic, logging, fallback behavior, and reconciliation processes before implementing integrations.
Privacy and Responsible Data Use
Responsible data governance includes respecting privacy and using data only for legitimate business purposes. Closeloop encourages privacy-conscious design by collecting only required data, limiting access to sensitive information, masking or encrypting data where appropriate, and avoiding unnecessary exposure in reports, logs, exports, or user interfaces.
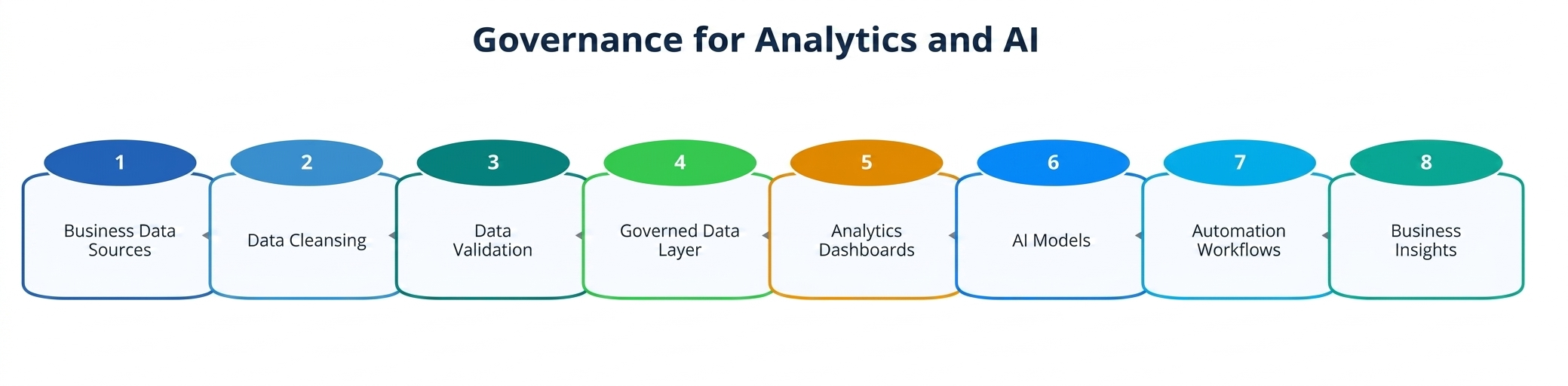
Governance for Analytics and AI
AI and analytics systems are only as reliable as the data behind them. Closeloop ensures that data used for dashboards, reporting, predictive analytics, personalization, or AI-powered workflows is properly structured, validated, governed, and monitored.
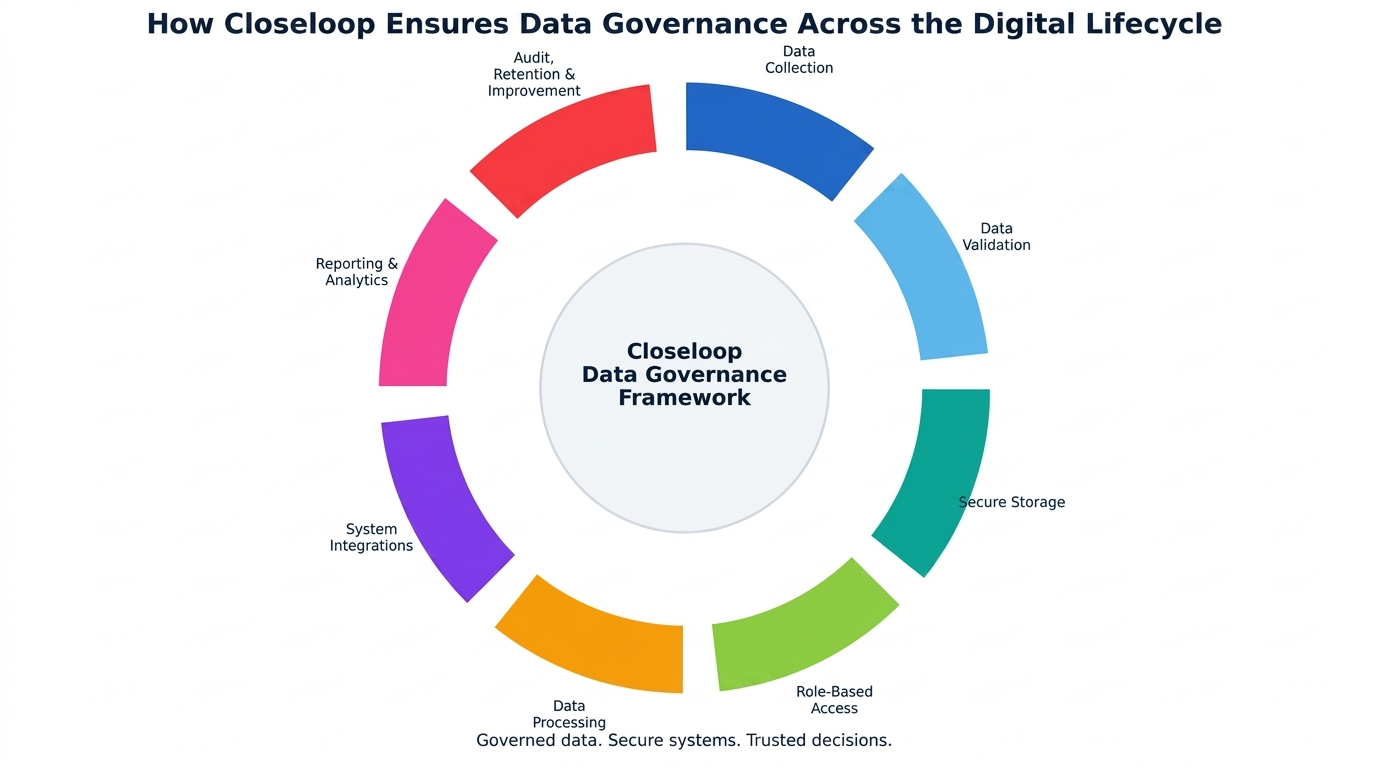
How Closeloop Ensures Data Governance Across Projects
Governance Starts During Discovery
Data governance begins before development starts. During the discovery phase, we work to understand the client's business processes, data sources, user roles, compliance needs, reporting expectations, and integration requirements. We identify what data the system will collect, where it will come from, how it will be used, who will access it, and what controls are required.
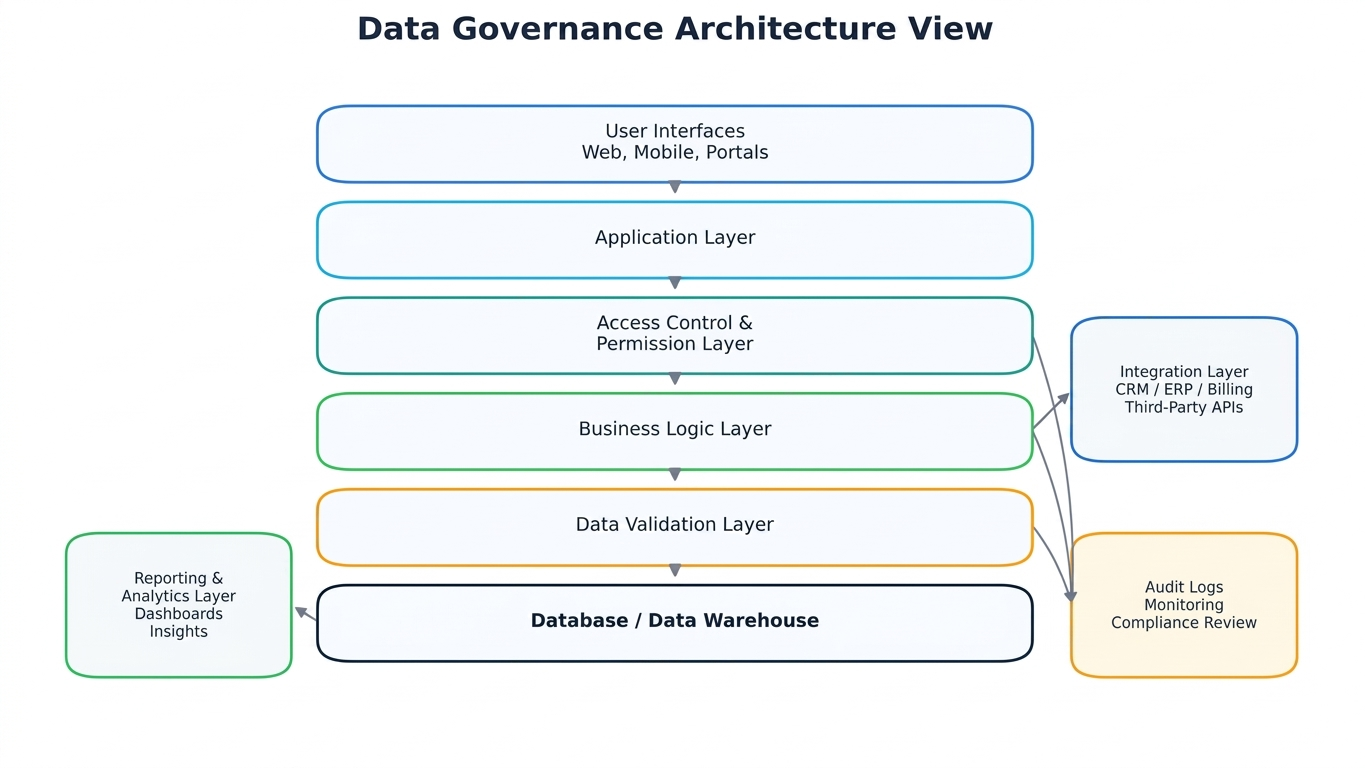
Data Models Are Designed With Structure and Scalability
A strong data model is the foundation of reliable governance. Closeloop designs databases, entities, relationships, and data flows with long-term scalability in mind. We define key objects, mandatory fields, validation rules, relationships, constraints, indexing needs, and reporting considerations.
Access Controls Are Built Into the Application
We implement role-based permissions and access rules directly into the application architecture. This ensures that different users have different levels of access based on their responsibilities, reducing both risk and operational complexity.
Data Movement Is Controlled and Monitored
When data moves between systems, Closeloop ensures that integration workflows are secure, documented, and monitored. We use secure API communication, authentication methods, error logging, data mapping, and reconciliation checks to ensure data is transferred accurately.
Sensitive Data Is Protected
Closeloop applies additional safeguards for sensitive data. This may include encryption, masking, restricted views, secure storage, secure transmission, and controlled exports. We also ensure that sensitive data is not unnecessarily displayed in logs, reports, or notifications.
Reporting and Dashboards Use Governed Data
Business users rely on reports and dashboards to make decisions. Closeloop ensures that reporting systems are based on accurate, consistent, and well-defined data sources. We help define metrics, calculation logic, filters, ownership, and access controls for dashboards.
Testing Includes Data Governance Checks
Testing is not limited to functionality. We also validate data behavior, including whether permissions are enforced, records are updated properly, integrations are syncing as expected, audit logs are working, and sensitive data is protected.
Documentation Supports Long-Term Governance
A system is easier to govern when it is properly documented. Closeloop provides documentation around data flows, roles, permissions, integrations, technical architecture, admin processes, and operational workflows.
Continuous Improvement After Go-Live
Data governance is not finished after launch. Closeloop supports continuous improvement by helping clients review access controls, optimize workflows, improve reporting, refine integrations, strengthen security, and adapt governance practices as the business grows.
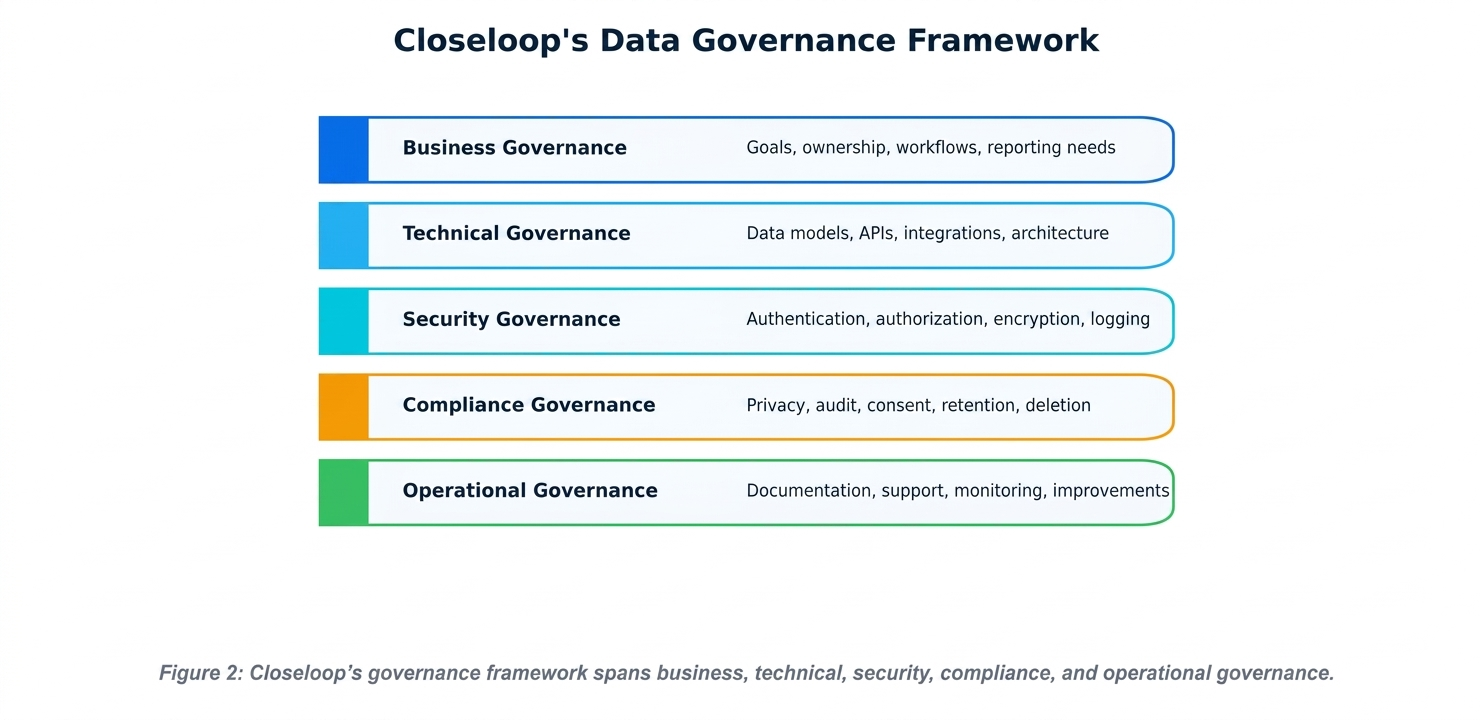
Closeloop Data Governance Framework
| Governance Layer | Purpose |
|---|---|
| Business Governance | Aligns data with business goals, ownership, workflows, reporting needs, and decision-making requirements. |
| Technical Governance | Designs secure, scalable, and structured systems that manage data consistently across applications, databases, APIs, and integrations. |
| Security Governance | Applies authentication, authorization, encryption, logging, monitoring, and secure development practices. |
| Compliance Governance | Supports regulatory readiness through privacy controls, auditability, consent management, retention rules, and secure access practices. |
| Operational Governance | Keeps data reliable after go-live through documentation, support, monitoring, maintenance, and continuous improvements. |
Conclusion
Data governance is no longer optional. It is a critical foundation for secure, scalable, and intelligent digital transformation.
At Closeloop, we ensure data governance by embedding it into every stage of solution delivery — from discovery and architecture to development, testing, deployment, and continuous improvement. Our approach focuses on ownership, quality, security, compliance, privacy, integration control, auditability, and responsible data use.
As businesses continue to adopt cloud platforms, automation, analytics, and AI, the importance of governed data will only increase. Closeloop helps organizations build systems where data is not only collected and stored, but protected, trusted, and used with purpose.
Stay abreast of what's trending in the world of technology
Source of Truth Systems at Closeloop
Modern businesses rely on multiple digital platforms to manage customers, products,...
Query Optimization in Modern Data Systems
In today’s data-intensive enterprise landscape, query performance is no longer a purely...
HIPAA Compliance Done Right: How Closeloop Secures PHI at Every Layer
Healthcare software carries one of the highest compliance burdens in tech. A single...
Controlling the Bill: A Company-Wide Guide to AI Cost Precautions
Artificial intelligence tools are now embedded in nearly every...